Insurance companies are witnessing a rise in fake domain registrations and cloned customer portals designed to harvest policyholder data, according to the India Cyber Threat Report […]
Tag: Cyber Attacks
Data Breaches in India’s Banking Sector in 2025: A Comprehensive Analysis
Executive Summary As India accelerates its digital transformation in banking and financial services, we face an unprecedented cybersecurity crisis that threatens not just individual institutions […]
Cybercriminals Step Up Attacks During the Holiday Online Shopping Rush
Every year, the holiday season brings a predictable spike in online activity. But in 2025, the volume of newly created malicious infrastructure, account compromise activity, […]
India Records265 million Cyber Attacks
Seqrite, the enterprise arm of Quick Heal Technologies Limited, a global cybersecurity solutions provider, has released the India Cyber Threat Report 2026 along with two […]
AI-Powered Cyber Weapons: How DDoS Attacks Have Become Geopolitical Precision Strikes
The cyber battlefield has undergone a dramatic transformation. With over 8 million DDoS attacks recorded in just the first half of 2025—including record-breaking 3.12 Tbps […]
Rapid Response Strategies for Cyber Attacks
Cyberattacks have evolved into sophisticated, coordinated threats targeting businesses, governments, and critical infrastructure. Attackers leverage AI-powered malware, ransomware, and supply chain vulnerabilities to breach even the […]
Phishing gangs use split and nested QR codes to evade detection in a new wave of ‘Quishing’ attacks, uncovers Barracuda
Barracuda threat analysts have uncovered two innovative techniques being used by cyber attackers to help malicious QR codes evade detection in phishing attacks. The techniques, […]
Veeam Launches Major Initiative to Train 100,000 Cyber Professionals as India Faces Security Crisis
Government officials and industry leaders gathered in New Delhi to address India’s escalating cyber security challenges, with authorities warning of a massive skills shortage as […]
Coveware by Veeam Reveals Q2 2025 Ransomware Surge: Social Engineering and Data Exfiltration Drive Record Payouts
Coveware by Veeam, the leading authority in ransomware response and cyber extortion trends, today unveiled its Q2 2025 ransomware report, spotlighting a dramatic escalation in […]
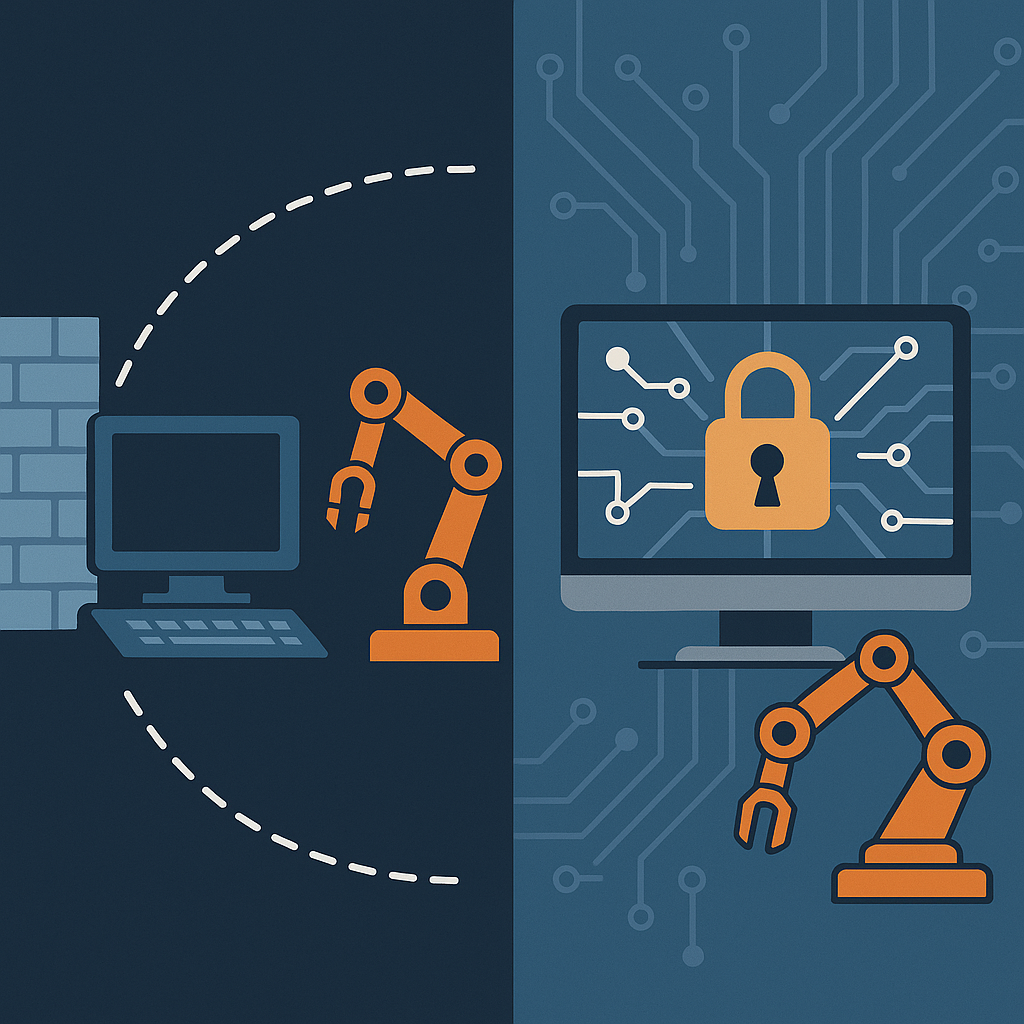
From Air-Gapped to Always-On: Securing Legacy OT Systems in Modern Manufacturing
Prior to the Industry 4.0 era, the Operational Technology (OT) ecosystem had limited cybersecurity risks as they were isolated from external networks and the internet. […]